Practical Steps for Third-Party Risk Assessment
Collaboration and outsourcing are fundamental for any business’s success in today’s world. Third-party risk assessment has emerged as a critical line of defense against potential vulnerabilities.
Outsourcing to a Third-Party Risk Management(TPRM) platform helps businesses in all industries be responsive and agile in a disruptive environment and may even provide them with a competitive advantage.
What’s more? Third-party risk modules within Governance, Risk, and Compliance (GRC) platforms are becoming more popular, with a 32% increase in adoption yearly.
This blog will give you better insights into the important steps in third-party risk assessment.
What is a Third-Party Risk Assessment?
Third-party risk assessment is the systematic process of identifying, evaluating, and managing the risks associated with outsourcing relationships and partnerships with external vendors, suppliers, or service providers.
By implementing a robust third-party risk assessment process, organizations can protect themselves from potential disruptions, data breaches, and compliance issues, ultimately enhancing their resilience and ensuring long-term success.
Steps to Conduct a Third-Party Risk Assessment
You can't completely eliminate all vendor risk, but you can manage it by assessing all the risks associated with each vendor as part of your due diligence process. A vendor risk assessment is an audit of the vendor's processes, policies, and financial health. It helps you understand how much risk you'll take when working with a specific vendor.
Usually, vendor risk assessments include the following steps:
Step 1. Identify the Vendors You Want to Assess
Create a comprehensive inventory of your organization's third-party vendors. Once you have this list, classify each vendor according to their criticality to your operations.
Categories might include critical, high, medium, and low risk based on factors such as the services they provide, their impact on business continuity, and the potential financial or reputational repercussions of a failure in service. This classification will enable you to focus your resources on vendors with the highest risk.
Step 2. Utilize Relationship Questionnaires and Risk Profiles
To gain deeper insights into the nature of your relationships with vendors, create questionnaires that assess various aspects of their operations, such as financial stability, compliance with regulations, data security measures, and previous incidents. You can create it in-house, use a resource you find online, or take advantage of vendor risk management software.
You should use this questionnaire to learn more about your vendors' policies, processes, and procedures and determine their additional risks. The data collected can also assist in determining which vendors may require more rigorous monitoring or due diligence.
Step 3. Examine and Analyze the Results
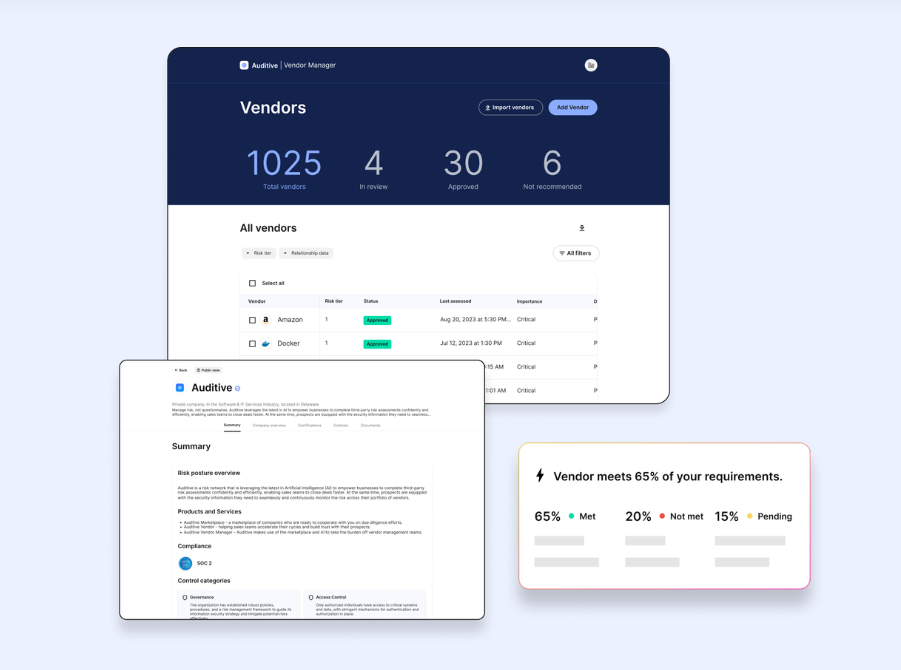
Once each vendor has submitted their assessment, it’s essential to review their responses and analyze the findings. Third-Party Vendor Management (TPRM) Platforms, like Auditive, help you do this seamlessly. Assign a risk rating to each vendor based on the level of risk they present and the number of potential risks they could pose to your organization.
Auditive: Continuous risk management for everyone
Step 4. Take Action Based on the Results
Evaluate the risks associated with each vendor and determine the appropriate risk management strategies needed to mitigate these risks. Often, you will need to ask the vendor to address any major concerns identified. In some instances, requesting an on-site audit can provide deeper insights into the vendor’s operations for a more thorough evaluation.
In rare cases, it may be necessary to eliminate the vendor from your list entirely, particularly in high-risk situations where mitigating measures are insufficient.
Step 5. Request Risk Assessments on a Regular Cadence
You may also choose to conduct additional assessments on a regular basis, depending on the vendor and their risk profile. These assessments could occur several times a year or as infrequently as once every few years.
Importance of Third-Party Risk Assessment
Third-party risk assessment is crucial for organizations that depend on external vendors, partners, or service providers. These assessments are vital for ensuring data protection, regulatory compliance, operational resilience, financial stability, and safeguarding a company’s reputation.
Here are the top 5 reasons why it is so important.
1. Protecting Data Security and Privacy
Third parties often have access to sensitive data, whether it's customer information, intellectual property, or other proprietary assets. If a vendor suffers a breach, it could expose your organization to data loss, legal liabilities, and reputational damage.
Regular third-party risk assessments help ensure that vendors have strong data security measures, are compliant with regulations like GDPR or CCPA, and are capable of protecting your data as you would.
2. Compliance with Regulatory Requirements
Many industries are governed by strict regulations that require organizations to manage third-party risks. Financial services, healthcare, and other sectors with strict privacy laws mandate regular risk assessments of vendors to ensure compliance. Failure to meet these requirements can result in heavy fines, sanctions, and loss of business licenses. Conducting thorough third-party risk assessments helps organizations avoid these penalties by verifying that their partners adhere to applicable regulations.
3. Preventing Supply Chain Disruptions
If a critical vendor fails or experiences operational issues, it can cause major disruptions to your supply chain. Third-party risk assessments help you identify weak points in your supply chain and evaluate whether your partners have the necessary continuity plans in place. This reduces the likelihood of interruptions due to financial instability, cyberattacks, or operational challenges that your vendors might face.
4. Mitigating Financial Risks
Vendors that are financially unstable or subject to economic risks can expose your organization to potential losses. For instance, a third-party provider going bankrupt could leave your company without crucial services or goods. Conducting a thorough assessment of a vendor's financial health and creditworthiness can prevent unexpected financial impacts by allowing you to identify and mitigate risks before they escalate.
5. Safeguarding Reputation
The actions or failures of third-party vendors can directly impact your brand's reputation. For example, if a vendor’s poor labor practices, environmental violations, or unethical business conduct become public, it may tarnish your organization’s image by association. A comprehensive risk assessment helps organizations vet their vendors’ practices, ethics, and compliance with social, environmental, and governance (ESG) standards, helping to protect their public image and corporate responsibility efforts.
What Does Third-Party Risk Assessment Involve?
It's crucial to recognize that managing third-party risks isn't just about identifying potential vulnerabilities. It’s about creating a comprehensive approach that evaluates both the strategic and operational impacts of those risks on the organization. By thoroughly assessing these areas, organizations can better anticipate, mitigate, and respond to the risks posed by external partners.
Managing Risks and Taking Action
Third-party risks are dynamic and require continuous attention. By establishing a solid framework, organizations can ensure they remain vigilant, adaptable, and ready to respond to emerging threats while maintaining strong third-party relationships.
Determine Management Strategies for Identified Risks: Effective third-party risk management involves a proactive approach to identifying and addressing potential threats posed by external partners. Once risks are identified, organizations must develop targeted management strategies tailored to each specific risk.
This begins with determining appropriate strategies that could include risk mitigation measures, enhanced monitoring protocols, or alternative sourcing options.
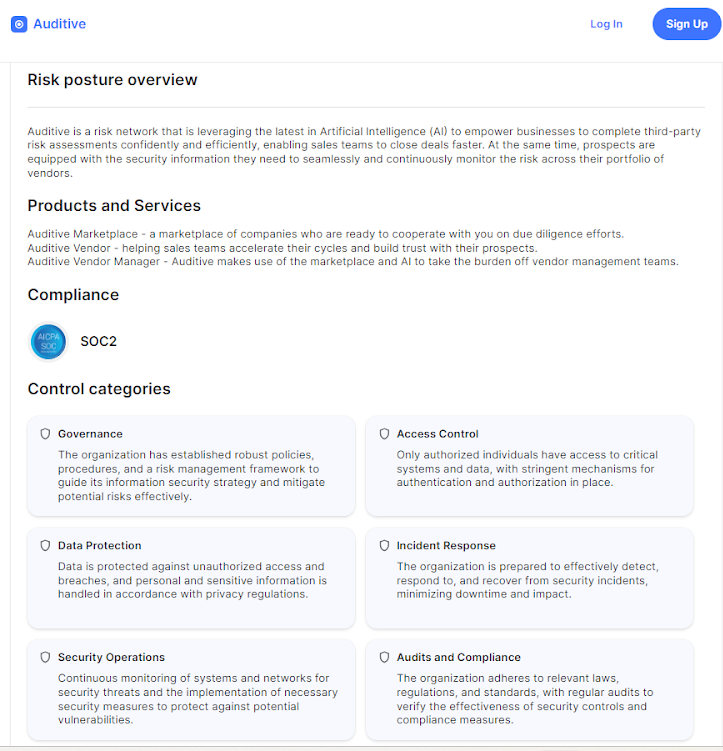
Implement Supplier Remedies or Audits as Needed: It is crucial to implement supplier remedies or conduct audits as necessary. TPRM platforms, like Auditive, have Trust Centers that help you close deals with transparent due diligence.
Regular audits can provide valuable insights into a vendor’s operations, compliance, and overall risk profile, ensuring they meet the organization’s standards and requirements. If issues are uncovered, organizations should work collaboratively with suppliers to rectify deficiencies, establishing clear timelines and expectations for remediation.
Consider the Removal of High-Risk Vendors: In cases where a vendor poses a significant risk that cannot be adequately mitigated, organizations must consider the necessary step of removing high-risk vendors from their supply chain. Do a thorough evaluation of the potential impacts on the business, weighing the risks against the benefits of maintaining the relationship.
Continuous Monitoring and Reassessment
In the dynamic landscape of third-party risk management, continuous monitoring, and reassessment are vital to ensure that organizations remain agile and prepared for emerging threats. Organizations can promptly address vulnerabilities and adapt to changing circumstances by establishing a robust framework for ongoing evaluation.
1. Schedule Regular Reassessments Based on Risk Profiles
To effectively manage third-party risks, it is crucial to maintain a diligent approach that evolves with changing circumstances. Regular reassessments help identify new threats and ensure that risk management strategies remain aligned with the organization's objectives and regulatory requirements.
Risk Profile Evaluation: Categorize third-party vendors according to their risk profiles, considering factors such as financial stability, regulatory compliance, and operational dependencies.
Regular Intervals: Establish a schedule for reassessments based on the risk level; higher-risk vendors may require more frequent evaluations, while lower-risk ones could be reassessed less often.
Trigger Events: In addition to regular intervals, monitor for significant changes in the vendor’s operations, financial status, or external market conditions that may necessitate immediate reassessment.
2. Update Risk Evaluations and Monitoring Systems Regularly
Maintaining a robust risk management framework becomes increasingly vital as organizations navigate the complexities of third-party relationships. To ensure that risks are accurately identified and effectively managed over time, it's essential to regularly update risk evaluations and monitoring systems.
Data-Driven Insights: Utilize analytics and data from ongoing monitoring efforts to update risk evaluations, ensuring they reflect current information and potential vulnerabilities.
Feedback Loops: Create mechanisms for capturing feedback from internal stakeholders and external audits, which can provide insights into potential gaps in the existing risk management framework.
3. Adapt Strategies to New Risks and Regulations
As the landscape of third-party risks continues to evolve, organizations must remain agile and responsive. Adapting strategies to address emerging risks and shifting regulatory requirements is crucial for maintaining compliance and protecting business interests. Here are some key considerations for effectively navigating this changing environment.
Regulatory Compliance: Stay informed about regulation changes that may impact third-party relationships, ensuring that risk management strategies align with the latest legal requirements.
Emerging Risks: Actively monitor industry trends and emerging risks, such as cybersecurity threats or geopolitical issues, adapting strategies accordingly to mitigate potential impacts.
Flexible Approaches: Foster a culture of flexibility within the organization, encouraging teams to proactively adapt risk management strategies in response to new information or evolving risk landscapes.
Utilize Technology for Risk Assessment
For organizations today, employing technology becomes essential in enhancing efficiency and accuracy in risk assessments. By integrating advanced tools and data analytics into risk assessment, organizations can gain deeper insights and make more informed decisions regarding their third-party relationships.
Here are the top 3 ways to utilize technology for risk assessment.
1. Implement Threat Monitoring and Risk Management TPRM Software
Implementing specialized TPRM software for threat monitoring allows organizations to track and analyze potential risks associated with third-party vendors continuously. Auditive is one such noteworthy tool. It is a risk management network that leverages the latest in Artificial Intelligence (AI). This technology empowers businesses to complete third-party risk assessments confidently and efficiently, which enables sales teams to close deals faster.
In fact, a report by Global Market Insights shows that AI can analyze large data sets to detect anomalies and predict potential risks.
2. Automate Assessment Processes for Efficiency
Automation plays a vital role in streamlining risk assessment procedures. By automating routine tasks, such as data collection, risk scoring, and reporting, organizations can significantly reduce manual effort, minimizing human error. This efficiency speeds up the assessment process and frees up valuable resources.
3. Centralize Data for Better Decision-Making
Centralizing risk-related data in a unified platform enhances visibility and accessibility for decision-makers. Organizations can develop a comprehensive view of their risk landscape by consolidating information from various sources, such as vendor assessments, compliance documentation, and incident reports. Auditive helps you streamline security reviews for both parties (sellers & buyers). This centralized approach facilitates better collaboration among stakeholders and enables data-driven decision-making.
A study by EY shows that 90% of organizations are moving toward centralized risk management. With a holistic understanding of risks, organizations can prioritize their responses, allocate resources effectively, and ensure that third-party engagements align with their risk management objectives.
Incorporating these technological strategies strengthens the overall risk assessment process and positions organizations to adapt swiftly to new challenges in the third-party risk environment.
Accelerate Your Organization’s Third-Party Risk Assessment Process with Auditive
Third-party risk assessments are crucial for safeguarding organizations against potential vulnerabilities that arise from external partnerships. As businesses increasingly rely on third-party vendors for various services, a robust risk assessment process is essential to identify, evaluate, and mitigate potential threats.
Moreover, ongoing risk management is not a one-time effort but a continuous process. Implementing a TPRM platform like Auditive allows you to access advanced tools for continuous threat monitoring, automated assessments, and centralized data management.
Auditive helps with regularly reviewing and updating your risk assessment protocols, which will empower your organization to adapt swiftly to any challenges and build resilience in today’s dynamic business environment.
Don’t leave your organization vulnerable. Schedule a Demo to strengthen your third-party risk management strategies today!